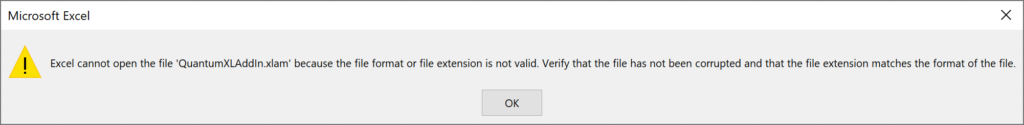
While the "file format or file extension is not valid" error is typical, some users have also reported the error "QuantumXLAddIn.xlam is not a valid add-in" or a Windows Security Popup "Action Blocked: Your administrator caused Windows Security to block this action. Contact your help desk" which has the same root cause and workaround.
Root Cause — Windows Defender Security Setting and Misleading Error Reporting
When Attack Surface Reduction (ASR) rule {D4F940AB-401B-4EFC-AADC-AD5F3C50688A} — "Block all Office applications from creating child processes" or rule {92E97FA1-2EDF-4476-BDD6-9DD0B4DDDC7B} — "Block Win32 API calls from Office macros" — is enabled, Quantum XL will be prevented from running. Unfortunately, Windows does not clearly indicate this. When Excel attempts to load the add-in, the ASR rule silently blocks execution. Because this happens before macro startup is complete, Excel throws a generic error stating that the file format or extension is not valid, which obscures the true cause.
Quantum XL uses Win32 API calls to store user settings, determine the user's locale, along with other functions. ASR GUID {92E97FA1-2EDF-4476-BDD6-9DD0B4DDDC7B} — "Block Win32 API calls from Office macros" is triggered when this occurs, causing the error.
Quantum XL opens Microsoft Word as part of its functionality which is blocked by ASR GUID {D4F940AB-401B-4EFC-AADC-AD5F3C50688A} — "Block all Office applications from creating child processes".
The update of Windows Security and Microsoft Defender Endpoint service security intelligence build 1.381.2140.0 released on January 13, 2023 was the first to provide the option to "Block Win32 API calls from Office macros".
